Passwords are still the most common way people log into apps and websites. Because of this, protecting passwords is one of the most important tasks in software development. This is where bcrypt comes in.
In this guide, you’ll learn what bcrypt is, how it works behind the scenes, and why it is trusted for secure password hashing and verification.
What Is Bcrypt?
Bcrypt is a password hashing algorithm designed to protect passwords even if a database is stolen. Instead of storing plain passwords, bcrypt converts them into long, unreadable strings called hashes.
Unlike basic hashing methods, bcrypt is intentionally slow. This makes it very hard for attackers to guess passwords using brute-force or dictionary attacks.
Hashing vs Encryption (Why It Matters)
Before going deeper, it’s important to understand one key idea.
Encryption can be reversed using a key.
Hashing cannot be reversed.
Bcrypt uses hashing, not encryption. This means once a password is hashed, it cannot be converted back to the original password. The only way to verify a password is to hash it again and compare the results.
How Bcrypt Hashing Works
When a user creates a password, bcrypt does much more than just hash it.
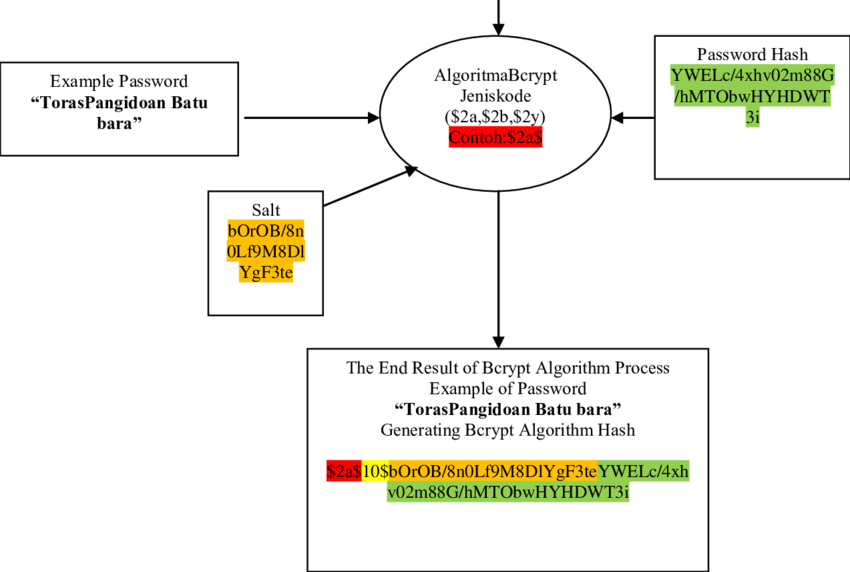
First, bcrypt generates a salt. A salt is a random value added to the password before hashing. This ensures that even if two users have the same password, their hashes will be different.
Next, bcrypt runs the password and salt through a process called key stretching. This means the hashing operation is repeated many times. The number of repetitions is controlled by a cost factor, also known as the work factor.
Finally, bcrypt outputs a single string that contains:
- the algorithm version
- the cost factor
- the salt
- the final hash
All of this is stored together in the database.
What Makes Bcrypt Secure?
Bcrypt is widely used because it was built specifically for password security.
One reason is its adaptive cost factor. As computers get faster, developers can increase the cost to make hashing slower and harder to attack.
Another reason is its strong resistance to rainbow table attacks. Since bcrypt uses unique salts for each password, precomputed attack tables become useless.
Bcrypt is also designed to be less effective on GPUs and specialized hardware, which attackers often use to crack passwords quickly.
How Password Verification Works with Bcrypt
When a user tries to log in, bcrypt does not decrypt anything.
Instead, the system takes the password entered by the user and hashes it again using the same settings stored in the database. If the new hash matches the stored hash, the password is correct.
This process is simple, secure, and does not expose the original password at any point.
Bcrypt vs Other Hashing Algorithms
Older algorithms like MD5 and SHA-1 are fast, which makes them unsafe for passwords. Attackers can try millions of guesses per second.
Bcrypt, on the other hand, is slow by design. This single difference makes it far more secure for real-world applications.
Newer options like Argon2 also exist, but bcrypt remains one of the most trusted and widely supported choices across programming languages and frameworks.
When Should You Use Bcrypt?
Bcrypt is ideal for:
- web applications
- mobile apps
- student projects
- startups and production systems
If you are learning backend development or building your first authentication system, bcrypt is a safe and practical choice.
Final Thoughts
Bcrypt works by combining salts, slow hashing, and adjustable cost factors to protect passwords from modern attacks. It does not rely on secrecy but on smart design that makes attacks expensive and time-consuming.
For students, developers, and anyone learning web security, understanding bcrypt is a big step toward building safer applications.
At techguide.ng, we believe learning security fundamentals like bcrypt helps you build better software and prepares you for real-world development challenges.