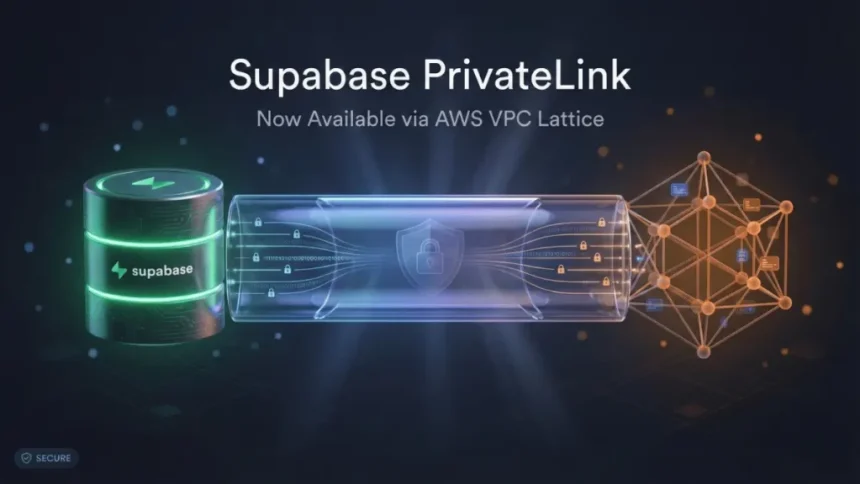
On January 26th, Supabase launched Supabase PrivateLink, a new feature that allows you to connect your Supabase database to AWS cloud resources using a private network.
In simple words, your database traffic no longer needs to pass through the public internet. It stays inside AWS.
That might not sound dramatic at first. But for companies handling sensitive data, this is a big deal.
Why Private Database Connections Matter
When you connect to a database normally, even if you use SSL and IP allowlists, the traffic still travels through public internet routes.
Yes, it is encrypted.
Yes, it is protected.
But it is still public-facing.
Security teams in industries like healthcare, finance, and government often ask:
“Can we connect to the database without using the public internet at all?”
Until now, that was complicated.
With Supabase PrivateLink, the answer becomes simple: yes.
What Is Supabase PrivateLink?
Supabase PrivateLink allows your Supabase Postgres database to behave as if it is inside your own AWS VPC (Virtual Private Cloud).
A VPC is simply your private section of AWS where your applications run.
When PrivateLink is enabled:
- Database traffic stays within AWS infrastructure
- No public internet exposure
- You can disable public database access completely
- Your attack surface becomes smaller
Fewer public endpoints mean fewer places attackers can target.
That’s not magic. That’s smart network design.
How AWS PrivateLink Works in Supabase
Supabase uses AWS VPC Lattice under the hood to power this feature.
Here’s what happens behind the scenes:
You enable PrivateLink in your Supabase dashboard. Supabase shares a VPC Lattice resource configuration with your AWS account. You accept the share, create an endpoint inside your VPC, and connect using a private DNS name.
Your applications then talk to the database through AWS’s internal infrastructure.
The connection supports:
- Direct Postgres connections
- PgBouncer for connection pooling
In many cases, latency is even lower than public connections because traffic takes a more direct AWS route.
So this is not only more secure. It can also be faster.
When Should You Use Supabase PrivateLink?
Not every project needs PrivateLink.
If you are building a small side project, SSL and IP allowlists may be enough.
But Supabase PrivateLink makes sense if:
You work in a regulated industry. Many compliance frameworks require private network connectivity.
You want to minimize your attack surface. Public endpoints always increase risk.
Your applications already run on AWS. If everything is already inside AWS, keeping traffic there is clean and efficient.
This feature is especially useful for teams building serious production systems that handle user data.
Current Limitations
Supabase PrivateLink is currently in Beta and has some restrictions.
First, it only works with AWS environments. Your workloads must run in AWS.
Second, it only supports database connections. It does not yet cover Supabase API, Auth, Storage, or Realtime services.
Third, your AWS VPC must be in the same region as your Supabase project.
Finally, it is available only on the Team and Enterprise plans.
So this is built for serious teams, not hobby deployments.
How to Set Up Supabase PrivateLink
If you understand AWS networking basics, setup is straightforward.
You add your AWS account ID in the Supabase dashboard under Settings and Integrations.
Then you accept the resource share in AWS RAM.
Next, you create a PrivateLink endpoint in your VPC and allow TCP port 5432 in your security group.
After that, you update your application’s connection string to use the private endpoint and test the connection using psql.
Once confirmed, you can disable public database access.
The full step-by-step walkthrough is available in Supabase documentation.
Why This Launch Matters
Cloud security is evolving.
Developers are no longer just building features. They are building secure systems that must pass audits, meet compliance standards, and protect sensitive data.
Supabase PrivateLink closes a major gap for teams that needed private VPC connectivity.
It makes Supabase more attractive for enterprise workloads, regulated industries, and security-focused teams.
This is not just a feature update.
It is a maturity signal.
Supabase is clearly positioning itself for serious production use.