In a perfect world, every developer would write secure code naturally. There would be no data leaks, no exposed API keys, and no forgotten passwords sitting inside code files.
But we do not live in that world.
Many companies still struggle with managing secrets like database passwords and API keys. Some developers even store these secrets in plain text files just to make their work easier. The problem is simple: if developers can access those secrets easily, attackers can too.
This is where shift-left security becomes important.
What Is Shift-Left Security?
To understand shift-left security, imagine a timeline of software development. On the left side, you have planning and coding. On the right side, you have testing, deployment, and maintenance.
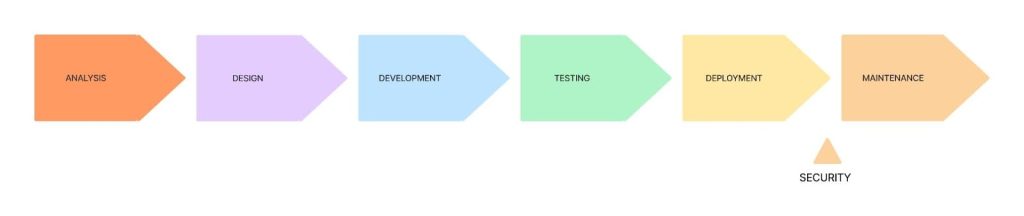
Traditionally, security checks happen near the right side usually just before production.
Shift-left security moves those security checks to the left side.
That means security starts early. Very early. From the first line of code.
Instead of waiting for a security team to review everything at the end, developers take responsibility from the beginning. This approach is also part of what many people call DevSecOps i.e combining development, security, and operations into one smooth process.
Why Shift-Left Security Matters
Fixing security problems late is expensive.
If a vulnerability is discovered after deployment, the company may lose money, reputation, and customer trust. Some reports show that organizations that experience secrets leakage can lose millions in revenue.
For junior developers, this lesson is powerful: the earlier you catch a problem, the cheaper and easier it is to fix.
Think of it like building a house. It is easier to fix a weak foundation during construction than after the building is complete.
Common Security Mistakes Beginners Make
Many beginner developers believe security is someone else’s job. They think, “The security team will handle it.”
But developers create the code. If insecure code enters the system, it becomes everyone’s problem.
One common mistake is hard-coding secrets directly into the code. For example, placing a database password inside a JavaScript file. This creates a security backdoor.
Another mistake is using different configurations in development and production environments. If your app works one way locally and another way in production, security gaps can appear.
These issues are avoidable.
How to Apply Shift-Left Security as a Beginner
Start by removing plaintext secrets from your code. Never store passwords or API keys directly inside your project files. Instead, use environment variables or secret management tools that encrypt sensitive information.
Next, make sure your development environment is as close as possible to your production environment. This is called environment parity. When both environments behave similarly, you reduce unexpected security issues later.
Modern developers also use secure SSH workflows. SSH keys should be encrypted and protected with two-factor authentication. Avoid storing private keys carelessly on your device.
Automation is another key part of shift-left security. Instead of manually checking for vulnerabilities at the end, use automated tools that scan your code for problems while you are still developing it. Many CI/CD pipelines can automatically run security checks before deployment.
Finally, always encrypt data in transit. This means using HTTPS and Transport Layer Security (TLS) so that data moving between client and server cannot be easily intercepted.
Reactive vs Proactive Security
Reactive security means waiting for something to break before fixing it.
Proactive security means preventing the problem before it happens.
Shift-left security is proactive. It encourages developers to think about vulnerabilities before they exist.
Even large companies automate sensitive processes to protect their secrets. They do not rely on one person to remember everything. They build systems that enforce best practices automatically.
That is the mindset junior developers should develop early in their careers.
Shifting Left Means Growing Up as a Developer
Shift-left security is not about fear. It is about responsibility.
When you write secure code from the beginning, you build trust. You reduce stress. You create stronger software.
For beginners, the lesson is simple:
Security is not a final step.
It is a starting point.
The earlier you think about it, the safer your applications become and the more valuable you become as a developer.